Introduction
Managing updates and patches for Virtual Machines (VMs) hosted in any enterprise environment is essential and can be a daunting task.
Patch management for VMs consist of frequent updates to the operating system such as anti-virus definition updates, operating system updates, software updates and much more depending on the system. There are many dependencies that will also need to be considered during this process such as; when the VMs can be updated, in what order the VMs should be updated as well as manually identifying the updates required.
Now, imagine all the above dependencies being managed for you, allowing you to control your enterprise environment and VMs efficiently through a simple portal. In this blog, I will be going over the Azure Automation Account and more specifically the Update Management feature offered to portray how easy patch management can really be.
Azure Automation Account – What is it?
Before jumping into Update Management, I want to provide a brief overview of the Azure Automation Account resource which is required for the Update Management feature to be enabled. Azure Automation Account helps to deliver a cloud-based automation service that can be utilised to manage both Azure and non-Azure environments. This resource consists of the following features:
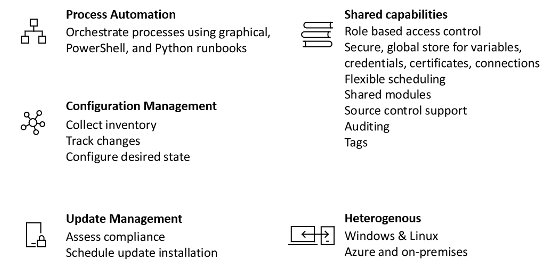
Figure 1: Overview of Azure Automation Account features
Each of the features mentioned above can be utilised together to provide the right automation process for your needs. For instance, it is possible to automate a process by creating a runbook and executing that runbook during a scheduled update installation. For example, this runbook can be simply checking to see if a dependant VM is running before the updates are carried out. Apart from that, the Automation Account is equipped with in-depth monitoring and alerting capabilities to help identify the status of each scheduled job.
All of the above features can be accessed through the creation of the Azure Automation Account through the Azure Portal or by using an Azure Resource Manager (ARM) Template deployed using PowerShell, Azure CLI or our preferred method which is Azure DevOps pipelines.
Update Management – How does it work?
Azure Automation includes the Update Management feature as mentioned previously. Update Management can be set up for both Windows and Linux systems across hybrid environments, making it a very powerful tool in large enterprise environments hosting multiple VMs. It enables users to create scheduled deployments, composing the installation of required system updates. The built-in features also enable you to exclude any updates if they shouldn’t be applied with the option of adding any pre-deployment or post-deployment scripts.
In order to set up Update Management for the first time, a Log Analytics workspace will need to be attached to the Automation Account. All monitoring solutions within Azure require a Log Analytic Workspace to store data collected by the solution, whilst also hosting the log searches and views. This workspace can be used for all features offered by the Automation Account.
To have a better understanding of how Update Management works, I will be walking through the different steps carried out. The below diagram will provide a brief overview of the process:
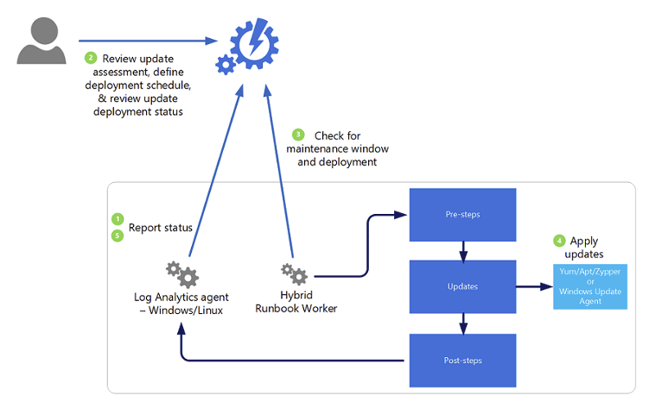
Figure 2: Visualisation of the Update Management process
As portrayed in the diagram above, there are five main steps that are carried out by the Update Management feature.
- The Log Analytics agent installed on the Windows/Linux VM will query the updates available for the VM and provide a report to the Automation Account. Information about the updates required is presented in the portal including the severity of the update.
- By referring to the Automation Account, users are able to review updates available for each attached VM and create deployment schedules for updates to be applied.
- In this step, the Hybrid Runbook Worker – a service that is installed on VMs after enabling Update Management – checks the Automation Account to gather information about the deployment schedules as well as the maintenance window defined.
- After gathering the required information, the Runbook Worker will proceed through the pre-step, updates and post-steps phases as defined in each schedule.
- Finally, after the updates have been completed, the status of each scheduled update is reported back to the Automation Account and stored in the Log Analytics Workspace.
Monitoring and Alerting
Data is everything when it comes to operations. Engineers need to be able to easily and efficiently query information in logs, whilst also being able to visualise such metrics to customers to create a story. Since a Log Analytics Workspace is mandatory for enabling the Automation Account, it means that data will be readily available for each VM that has been added to the Update Management service, this can include:
- Updates required for each VM
- Update status per VM
- Summary of schedules executed
- Number of VMs requiring an update
This data is also portrayed on the Update Management service of the Automation Account, providing a clear picture regarding the number of VMs requiring an update, as well as the classification of the updates required.
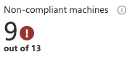
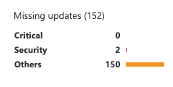
Figure 3: Compliance Report for VMs attached to update management
Most importantly, this data can be used to create critical alerts for the operation team. Alerting is crucial and enables a proactive approach when dealing with resources that are in the production environment. For instance, applying updates in production will without a doubt require a thorough change management process, therefore the update schedules cannot be set up to run automatically. But that doesn’t mean the team will have to spend time every day to see if VMs are in a non-compliance state. Through alerts, we can proactively be notified when updates are required and for which VMs, so teams can reduce the meantime to resolution (MTTR) when going through the change management process of running an updated schedule.
Other than that, alerts can be set up through the Log Analytics Workspace to notify the team of any failures during the execution of the schedule. This will undoubtedly help the team become more proactive when solving the issue.
Conclusion
Updating a virtual machine may not sound too daunting if you think of just one VM, but if the same task was to be carried out for hundreds of VMs at different times throughout the day or night, then it can be a living hell. The Update Management feature through the Automation Account provides a smooth transition into a scheduled based automated process of applying updates for cloud or on-premise VMs.
If you need help setting up automated patching for your virtual machines, feel free to leave a comment on this blog. We will be more than happy to assist you in this journey.

.jpeg)
.jpg?width=1920&name=rhys-KB9uIKWQN7I-unsplash%20(1).jpg)